You’ve got that funny feeling in the pit of your stomach that something isn’t quite right. You’ve logged into your Gmail account, but there are emails from places you don’t recognize and emails checked as “read” which you definitely haven’t read.
The more you think about it, the more you’re sure you’re not alone: someone else has been playing around in your Gmail account. All of your private information, potentially open to others.
Well, you don’t need to worry – here we’ve laid out everything you need to know:
- How to check your account activity,
- How to work out who is snooping around,
- How to stop them, and
- How to make sure your account is as safe and secure as it can be.
How Google makes it easy to check your account activity
How do you find out what’s been going on with your account? Who has been accessing it, what they’ve been doing, and where they’ve been?
First things first, here are the steps how you may check your account activity:
1) Log in to your Google Account.
2) On the left-hand side, you’ll find “Privacy & personalization”. Click on this.
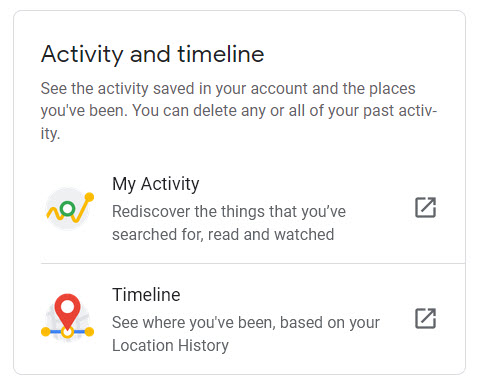
3) Then you’ll need to select “My Activity” under “Activity and timeline”.
4) Your activity will be listed here, with the day and time of any account activity.
5) You can use the search bar to filter and find out what was going on at a specific time.
One of Google’s more useful capabilities is keeping a record of when and from where your account has been accessed. This feature is called “Last Account Activity”.
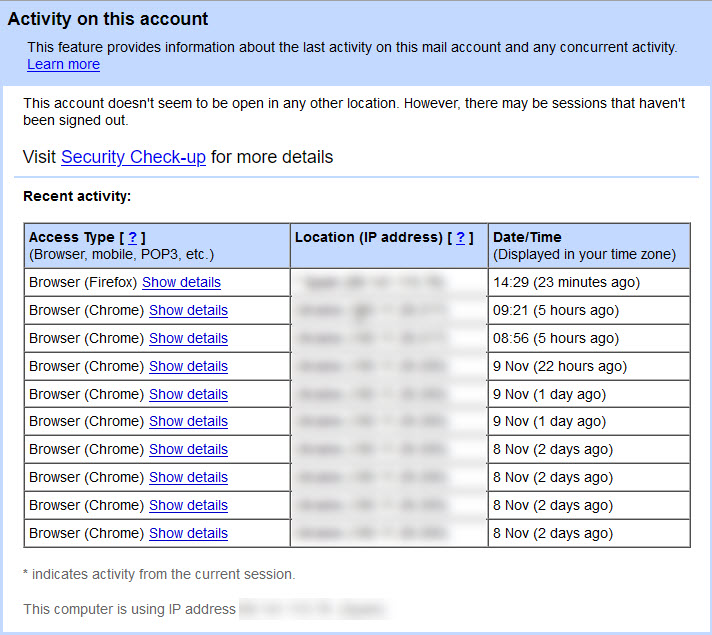
Once you’ve logged into your Gmail account, you can scroll down to the bottom of your inbox and find “Details” on the right-hand side of the page.
Clicking on this will bring up a new window that lists the following information:
- The IP address which accessed your account (this also indicates the country it came from),
- The date and time it was assessed, and
- Whether the access was through a browser, a mobile, or an authorized application.
Who’s trying to get into my Gmail account?
Now you’ve got your necessary information, and you can check through the list and look for any suspicious entries. Here’s what to look out for:
- Odd IP addresses (that are different from the ones you usually see),
- Odd times (when you were asleep, or definitely not near your computer), or
- Odd access types (maybe you only ever log into your account on a mobile device, and there’s browser access listed).
Spotting anything like this means it’s pretty likely someone has been messing around in your account. You are even able to tell from which IP address and which country the access attempt came from.
For more immediate information, you can find out which devices are currently logged into your account by logging into your Google Account (not your Gmail) and clicking on the “security” tab on the left-hand side of the page.
From here, you can do a security check, where Google will talk you through how to make your account more secure or any specific issues they have noticed.
Google will also automatically notify you of any activity on your account that is considered suspicious, usually via email.
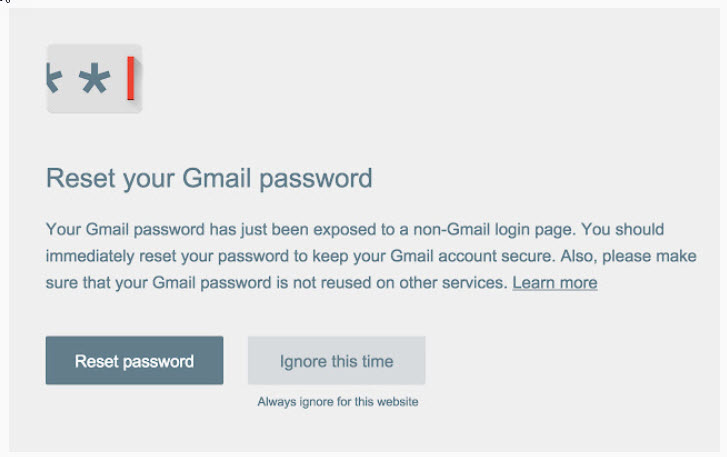
Besides, there are other protective mechanisms such as the Chrome extension Password Alert, which protects you against phishing. If your Google password has been used on a non-Google site, then you’ll be sent an alert and prompted to change your password.
Preventing other people from accessing my Gmail account
While you’re on the “Details” page of your account, you can press a button and immediately log out of your account from all locations.
Pressing this button will close access from all suspicious sessions on other devices and allow you to immediately change your password to something more secure.For a more targeted option, under the “Your Devices” section of Google Security, Google will show you which devices are signed in to your account and when they signed in.
It will also allow you to sign out any that you do not recognize or don’t want to access. Once you’ve done this, it is probably a good idea to change your password again.
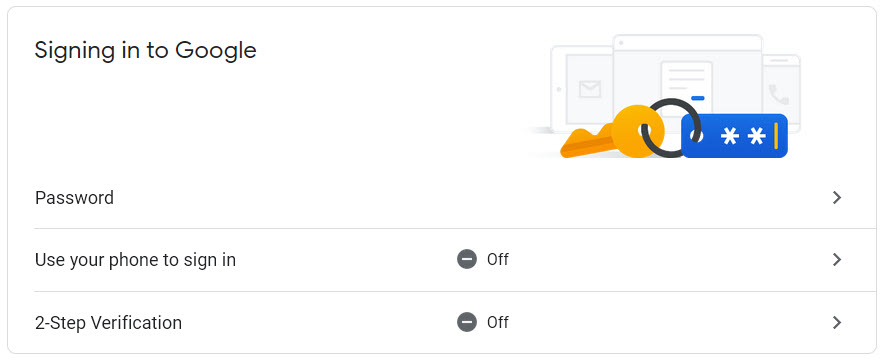
Changing your password
Changing your password is imperative if you think your account may have been accessed. This is also a good opportunity to create a more complex password, harder to guess or hack. And it’s effortless to do:
- Log in to the Google Security page,
- Click on “sign in to Google” and “password”,
- Enter your current password, and choose a new one.
Setting up 2-factor identification
As well as immediately changing your password, there is one other thing you can do. Two-factor identification makes your account even more secure. So, if you’re worried someone has been snooping around, then it offers you some peace of mind.
Each time you attempt to sign in to your account, you’ll need to enter your password, and then you’ll be sent a verification code to your authorized device, which you’ll need to enter before you can gain access.
This means that, in the unlikely event that someone guesses your new complex password, they still won’t have enough information to get into your account.
Here’s how to set it up:
- Head back to the Google Security page,
- Click “Signing into Google” and then “2-step verification”,
- Click “Get Started”, and you’ll be talked through the whole process.
How else can I tell if my Gmail account has been hacked?
With all the different passwords and log-in methods that we have to deal with in our digital world, it can sometimes seem impossible to work out if something is wrong.
But, in addition to the checks we’ve outlined above, there are a few other simple ways of finding out if your Gmail account has been hacked:
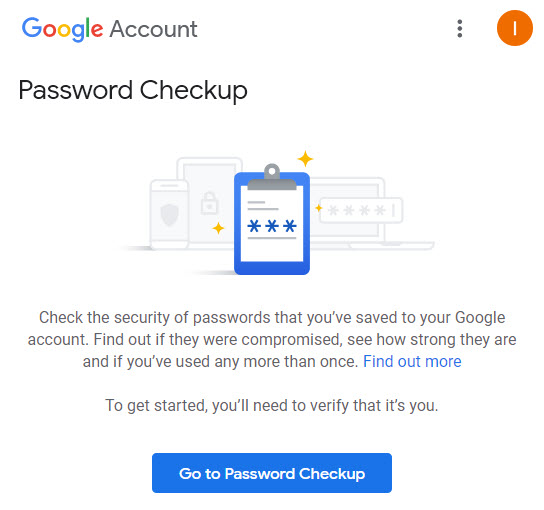
Download Password Checkup:
Last year, Google launched the Chrome extension “Password Checkup”. This add-on will sit in your browser and flag if you sign into any website using any password Google has on their “hacked list”, allowing you to change your passwords and keep your information secure.
Old-fashioned sleuthing:
Sometimes it is down to a gut feeling that something isn’t right. Some tell-tale signs that you don’t need a Chrome extension to include:
- Looking for emails unexpectedly in the deleted folder;
- Finding opened emails in your inbox that you don’t remember reading, or
- Getting notification emails from services you don’t use.
Any of these can be red flags that something is not quite as it seems and nudges that you need to beef up your account security in the ways we’ve talked about here.
Making sure my email is secure remotely
Once you’ve run through our instructions and checked all the security boxes, there are two things left to do to make sure your email is as secure as possible:
Signing out. Now you’ve changed your password and set up your 2-factor verification, and you need to sign out of all devices. That way, you’re the only person who has all the required information to log back into your account, which you can now do!
Running a malware and antivirus scan. If you’re concerned that you may have been subject to phishing attacks through your Gmail account, then using reputable antivirus software, run a comprehensive antivirus and malware scan on all of your devices.
Recovering your data
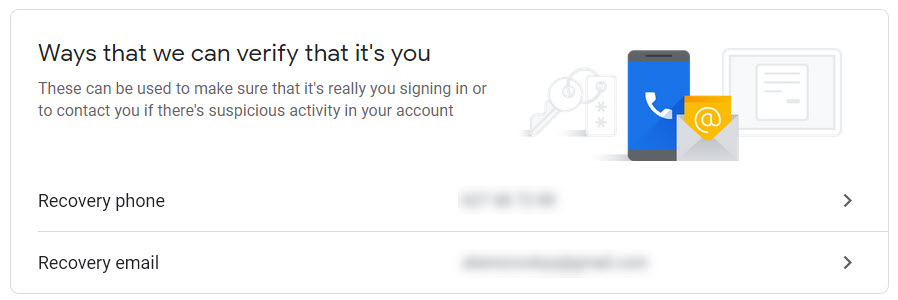
If the worst happens, and you are hacked, the hacker may have changed details such as your password or security question, and you may not be able to get into your email.
To prevent this from happening, you can set up a recovery email and recovery phone in the security section of your account.
Adding a different email address (with a strong password) and a phone number means that Google can send you a link to get back into your Gmail account and prompt you to change the password once more.
Here’s to feeling safe and secure
It’s a scary thought that someone might have been fishing around in your private digital spaces. But with a few simple tools, you can find out whether your Gmail account is being accessed, who’s butting their nose in, how to make your account super secure, and how to throw out unwanted intruders.
Now you can feel safe in the knowledge that you’ve done all you can for your digital security – go forth and browse freely!